Serverless computing is revolutionizing how applications are built and deployed, offering benefits like automatic scaling, reduced infrastructure management, and cost efficiency. However, these advantages come with unique security challenges that must be addressed to ensure the protection of serverless applications. This comprehensive guide explores best practices for securing serverless applications, covering essential aspects of serverless security and providing actionable insights to mitigate risks and enhance protection.
Understanding Serverless Security Challenges
Serverless computing introduces several security challenges that differ from traditional server-based environments:
- Increased Attack Surface: The distributed nature of serverless functions means there are numerous entry points and endpoints that can potentially be exploited. Each function, API endpoint, and third-party integration adds to the attack surface.
- Lack of Traditional Network Perimeter: Serverless functions are ephemeral and do not operate within a fixed network perimeter. This makes it challenging to apply traditional network security measures and firewalls.
- Shared Responsibility Model: In serverless computing, the cloud provider is responsible for the underlying infrastructure and some aspects of security, while the customer is responsible for securing their code, data, and access controls. Understanding this division of responsibilities is crucial for comprehensive security.
Best Practices for Serverless Security
1. Implement Least Privilege Access Control
Applying the principle of least privilege ensures that each serverless function and user has only the permissions necessary to perform their tasks. This minimizes the risk of unauthorized access and potential damage from compromised functions.
- Role-Based Access Control (RBAC): Define roles and permissions carefully. Create specific roles for different functions and services, granting only the permissions required for each role.
- Function Permissions: Configure minimal permissions for serverless functions to limit their access to resources. Avoid granting broad permissions that could expose sensitive data or services.
Example: In AWS Lambda, use IAM roles to grant functions access only to the specific S3 buckets or DynamoDB tables they need. Avoid using broad permissions like AmazonS3FullAccess when only AmazonS3ReadOnlyAccess is required.
2. Secure Function Code and Dependencies
The security of your function code and its dependencies is critical. Vulnerabilities in code or third-party libraries can be exploited by attackers.
- Code Reviews and Static Analysis: Regularly review your code and use static analysis tools to detect vulnerabilities, such as SQL injection, cross-site scripting (XSS), and insecure coding practices.
- Dependency Management: Keep dependencies up-to-date and scan them for known vulnerabilities. Utilize tools that can automatically update and patch vulnerabilities in your dependencies.
Example: Use tools like SonarQube or Checkmarx to perform static code analysis and identify security issues. Employ tools like Snyk or Dependabot to monitor and update dependencies.
3. Use Environment Variables Securely
Environment variables are often used to manage configuration and secrets in serverless functions. Handling these securely is crucial to prevent sensitive information leaks.
- Avoid Hardcoding Secrets: Do not hardcode sensitive data (e.g., API keys, passwords) directly into function code. Instead, use environment variables or dedicated secret management services.
- Encrypt Sensitive Data: Store sensitive environment variables securely and encrypt them to protect against unauthorized access.
Example: In AWS Lambda, use AWS Secrets Manager or AWS Systems Manager Parameter Store to securely manage and access secrets. Ensure that environment variables containing sensitive data are encrypted and only accessible by the functions that need them.
4. Secure Data Storage and Transmission
Data security is paramount both at rest and in transit. Implementing strong encryption practices helps protect sensitive data from unauthorized access.
- Encryption: Use encryption to secure data stored in databases, file systems, or object storage. Encrypt data transmitted over networks to protect it from interception.
- Secure APIs: Implement authentication and authorization mechanisms for APIs exposed by serverless functions. Use HTTPS to ensure secure data transmission.
Example: Encrypt data stored in AWS S3 buckets using server-side encryption and ensure all API communications are conducted over HTTPS to protect data in transit.
5. Implement Network Security Measures
Even without a traditional network perimeter, network security remains essential in a serverless environment.
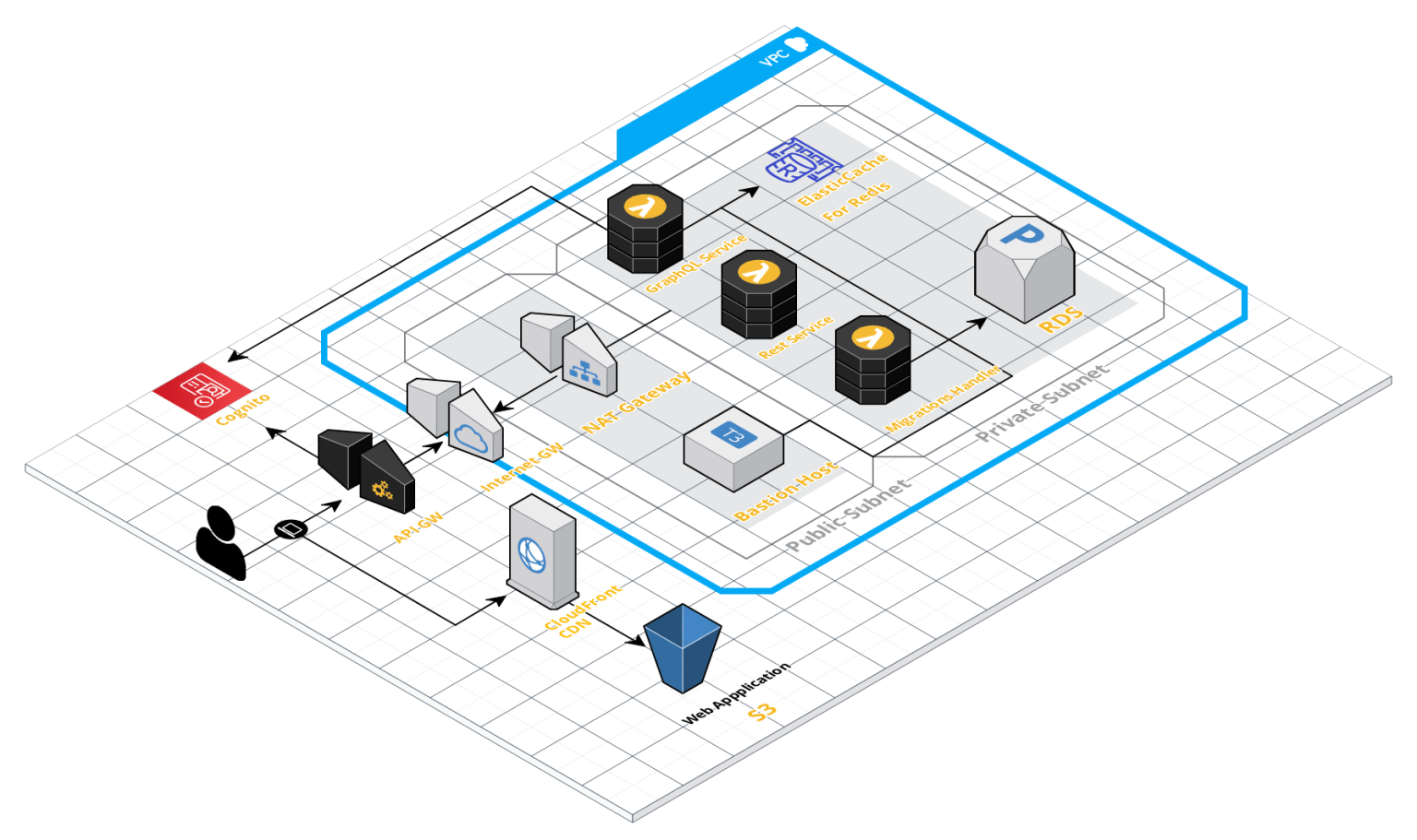
- VPC Integration: Use Virtual Private Cloud (VPC) integration to isolate serverless functions and control network access. Apply security groups and network ACLs to manage inbound and outbound traffic.
- API Gateway Security: Protect APIs exposed through services like API Gateway with authentication mechanisms, such as OAuth, API keys, or custom authorizers.
Example: Configure AWS Lambda functions to run within a VPC for added isolation and control. Use AWS WAF (Web Application Firewall) with API Gateway to protect against common web exploits.
6. Monitor and Log Activities
Effective monitoring and logging are crucial for detecting and responding to security incidents.
- Enable Logging: Ensure that logging is enabled for serverless functions and related services. Store logs securely and regularly review them to identify and investigate suspicious activities.
- Monitor Function Metrics: Use monitoring tools to track performance metrics, errors, and usage patterns. Set up alerts for anomalies or unusual behavior.
Example: Utilize AWS CloudWatch Logs to capture and review Lambda function logs. Configure CloudWatch Alarms to alert you to unusual spikes in function errors or invocation rates.
7. Implement Security Testing and Validation
Regular security testing helps identify and address vulnerabilities in serverless functions and associated services.
- Penetration Testing: Conduct penetration testing to uncover security weaknesses in serverless applications and their dependencies.
- Automated Security Scanning: Use automated tools to continuously scan serverless functions and infrastructure for security issues and compliance with best practices.
Example: Use tools like OWASP ZAP for penetration testing and continuous security scanning to identify vulnerabilities in your serverless applications.
8. Prepare for Incident Response
Having a well-defined incident response plan ensures that you can effectively manage and mitigate security incidents.
- Incident Response Plan: Develop and maintain a plan that includes procedures for identifying, containing, and mitigating security incidents. Ensure that the plan covers serverless-specific scenarios.
- Regular Drills: Conduct regular drills to test and refine your incident response plan. Simulate various security incidents to ensure your team is prepared.
Example: Create detailed playbooks for handling different types of security incidents, such as data breaches or unauthorized access, and regularly practice these scenarios with your incident response team.
9. Maintain Compliance
Compliance with relevant regulations and standards is crucial for avoiding legal and financial penalties.
- Compliance Requirements: Identify and adhere to compliance requirements, such as GDPR, HIPAA, or PCI-DSS, that apply to your serverless applications.
- Regular Audits: Conduct regular security audits to assess compliance and address any gaps or issues.
Example: Use AWS Artifact to access compliance reports and manage compliance with industry standards and regulations, ensuring that your serverless applications adhere to legal requirements.
10. Educate and Train Teams
Training and educating your team members on serverless security best practices is essential for maintaining a secure environment.
- Security Training: Provide regular training and awareness programs for developers, operations teams, and other stakeholders on serverless security principles and practices.
- Best Practices: Share and promote security best practices within your organization, ensuring that all team members understand their roles and responsibilities.
Example: Organize workshops and webinars on serverless security, and provide access to online resources and training materials to keep your team updated on the latest security practices.
Real-World Examples of Serverless Security Implementations
1. Financial Services
A financial services company leverages AWS Lambda for processing transactions. They implement least privilege access controls by restricting function permissions to specific S3 buckets and use AWS Shield for DDoS protection to safeguard their serverless functions.
2. E-Commerce Platform
An e-commerce platform integrates serverless functions with AWS API Gateway. They secure their APIs using OAuth and monitor function activities with AWS CloudWatch Logs to detect and respond to suspicious behavior.
3. Healthcare Provider
A healthcare provider utilizes Azure Functions to handle patient data. They implement strict access controls, manage secrets with Azure Key Vault, and ensure compliance with HIPAA regulations through regular security audits and encryption.
Challenges in Serverless Security
While serverless computing offers many advantages, securing serverless applications presents several challenges:
1. Complexity of Security Management
The distributed and dynamic nature of serverless environments can complicate security management and require new approaches and tools.
2. Dynamic and Ephemeral Nature
The ephemeral and dynamic nature of serverless functions makes it challenging to apply traditional security measures and maintain visibility.
3. Integration with Existing Security Tools
Integrating serverless functions with existing security tools and practices may require adjustments and additional configuration.
Conclusion
Securing serverless applications requires a proactive and comprehensive approach that addresses the unique challenges of the serverless model. By implementing best practices for access control, code security, data protection, network security, and monitoring, organizations can protect their serverless applications from potential threats. Regular security testing, incident response planning, and compliance maintenance are crucial for maintaining a robust security posture in a serverless environment. As serverless technologies continue to evolve, staying informed about emerging security practices and trends will help ensure the ongoing protection of serverless applications.
To learn more about our vision stay up to date with latest news and trends and how we’re making a difference, We invite you to OC-B by Oort X Media.